Category / IT
Great Experience with NZeTA App
Many countries now require visitors from supposed-to-be visa-free countries to apply for ETA (Electronic Travel Authority) or similar scheme before entering the country.
ETA is easier to obtain as compared to the visa. The former requires only online submission and the results would be made available within a short time, a few days max. However, filling up the form for the ETA – especially for the USA – may be quite daunting. It is not difficult but simply time consuming.
Until I applied for ETA for New Zealand, NZeTA. From 1 October 2019 New Zealand will require visitors from visa-free countries to obtain NZeTA prior to the travel.
The New Zealand Immigration provided two options to apply NZeTA: through web or mobile app. Interestingly, it costs NZD 3 less to apply using the app as compared to the web. Out of curiosity I chose to apply using the app.
Searching the on Google App Store (well, I am an Android user) app was easy. The installation was a breeze without any issues.
The application process was surprisingly easy. Upon opening the app, I was prompted with the welcome page.

Followed by acknowledgement for the usual privacy and term and use.

The next step caught me a bit off guard. It prompted me to take a picture of the passport.
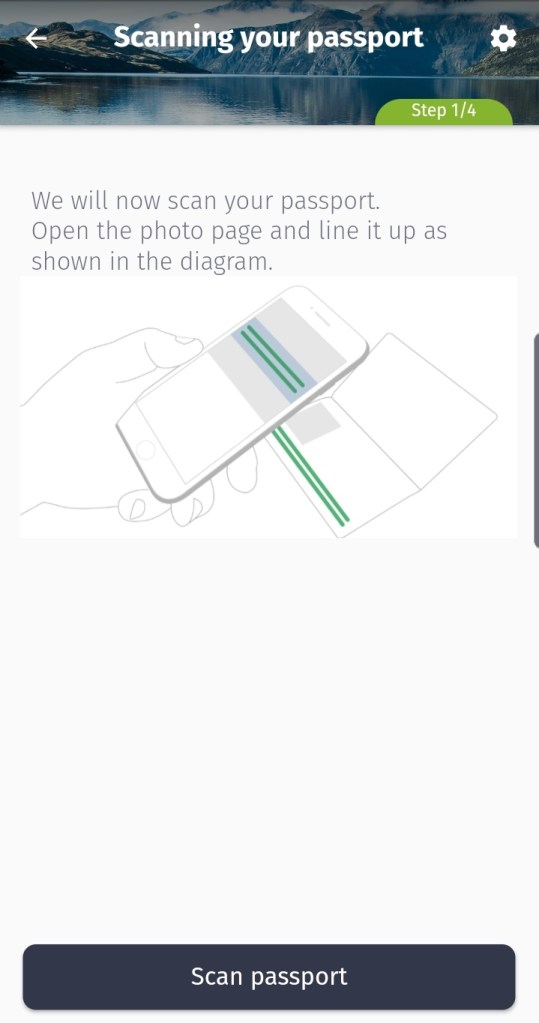
However, rather than taking the picture of the whole passport, the app actually scanned the Machine-Readable Zone (MRZ) area. The screen would show a blue bar where you should align the MRZ. As a result, capturing the MRZ was a breeze!

The next step was quite interesting, it asked me to do selfie!
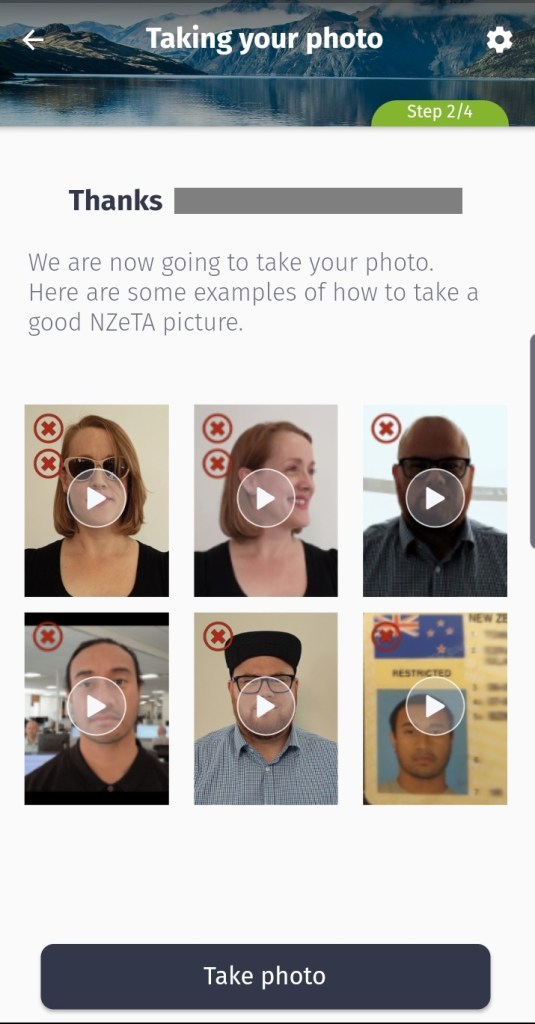
It took me a few attempts to do the selfie. Once completed, the app displayed the information captured from the MRZ, with the picture on the top-left corner. It asked me to confirm the details.

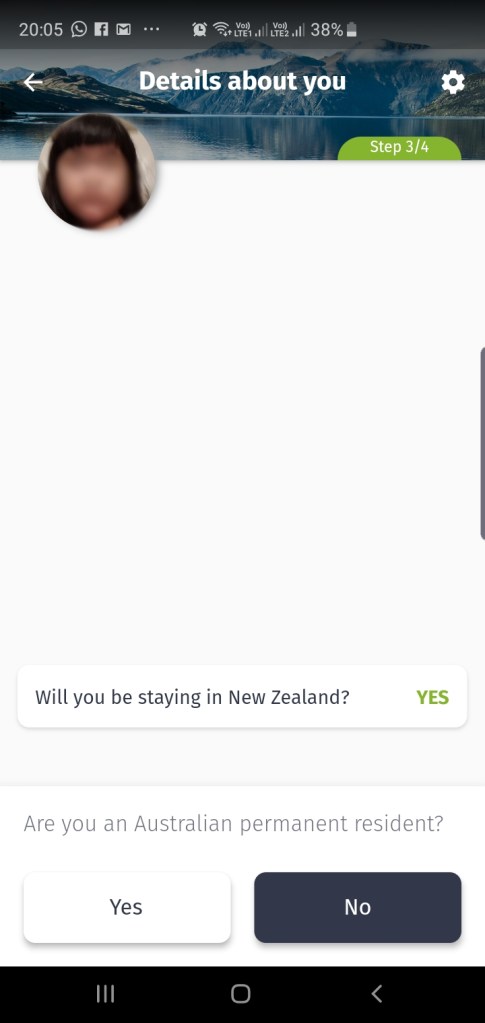
After that, the app asked a series of questions, starting from whether I want to stay in NZ or coming as a transit passenger, whether I am an Australian permanent resident, and so on. Interestingly, the ‘expected’ answer is always highlighted.

After answering all the questions, I proceeded to pay the ETA and the International Visitor Conservation and Tourism Levy (IVL). The payment was done using credit card and it was a fuzz free. I did not use the feature to take picture of the credit card – which I believe would help me to key-in the credit card details; I chose to key-in the card details myself. The only missing is there was no 2 FA for the credit card transaction.
And that’s it! The whole process was completed in less than 10 minutes, all from within the app itself. It was a great experience!
The app made it easy for anyone who applied for NZeTA. There was no need to upload any additional documents or pictures. The app also reduces or even eliminates error by using MRZ to fill up the details; no need for the applicant to type all the details manually.
The selfie is also interesting. There is no need for the applicant to rush to to instant photo booth or photo studio to take the picture, which would delay the whole application process.
The app practically eliminates all frictions in applying the NZeTA. It is a great innovation from The New Zealand Immigration. As a citizen, friction-less transactions such as what the app offered is the one I am looking for when transacting with the Government; and as a public servant such app is the yardstick for a good Government eServices.
Embracing Messiness
One day I was asked to draw how the applications we have are interfacing with other applications. It was a quite big task to come out with such diagram, but I managed to do it.
The diagram looks like this.
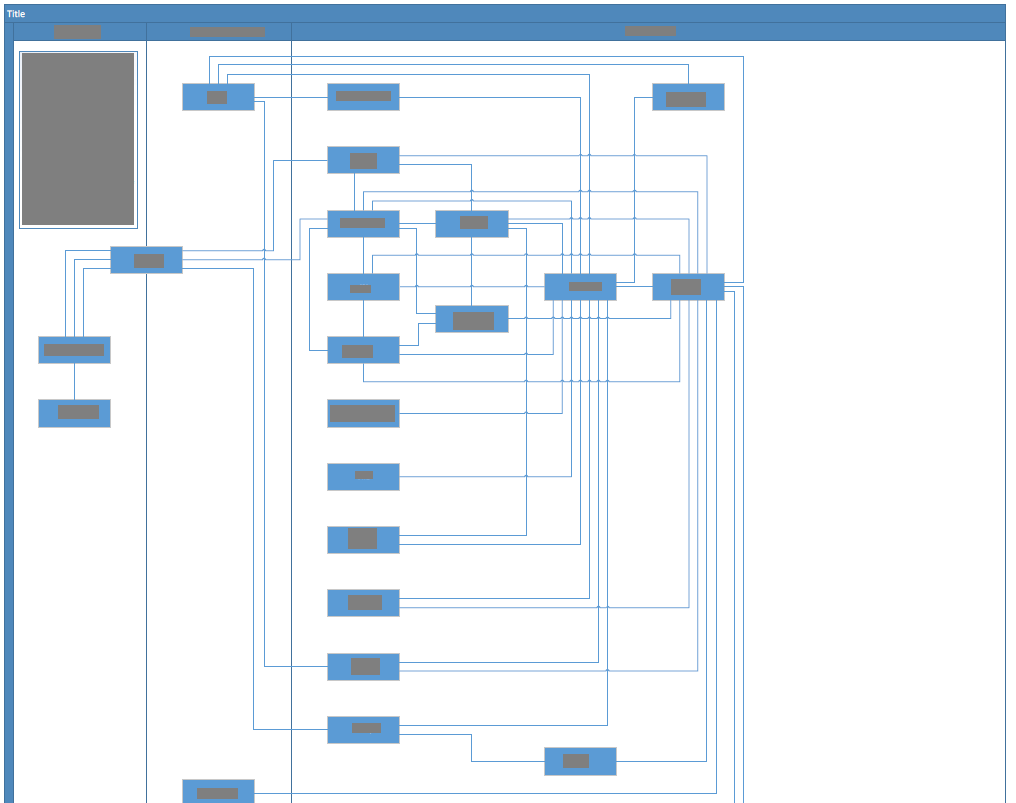
(of course, I need to remove the details)
When I presented the diagram, the most comments were about how messy the applications are.
I disagreed. Such messiness, in fact, should be EMBRACED.
Firstly, there is no application that can do all the functions that the organisation needs. An organisation typically uses different applications and integrate them at the back-end so that to achieve a good user experience across different applications.
When an organisation moves to the cloud, it opens up even more applications it can use. The integration between cloud-based applications (and also with Intranet-installed applications) would even be more pervasive.
With the advent of microservices and container, the integration would even more complex than typical application-to-application integration. A particular business function may be served by multiple microservices, each may call other microservices.
Microservices and container when combined with DevOps also introduces more complexity. If properly configured, a container can run in different hosting environment at different time, transparent to the user, but introducing a more (at least to what some people think of) another dimension of messiness (and complexity) as the service has no ‘permanent home’.
Trying to simplify the interfaces between applications would simply not work. What the organisation needs to do is to embrace such messiness with some measures to prevent chaos.
For a start, the organisation should put in place governance. The organisation should know what interfaces are being deployed, who is calling what, version, security, schema and which interfaces to be retired. This will also allow the organisation to better reuse existing interfaces, rather creating new ones.
However, governance itself is a rather tricky concept as may hinder application development. Governance implies set of rules that must be followed by developers otherwise there would be some kind of penalties. The scrum team may also see governance slowing down their works as they need to go through ‘review’ process. Some pragmatic approaches on governance needs to be applied.
The organisation may also consider to implement some systems, such as API Gateway or message queue to provide the layer of governance on interfaces. It also provides additional layer of security with the cost of additional complexity and reduced reliability as such systems may become a single-point of failure in the whole organisation.
Data governance is also important. An entity should have consistent data structure throughout organisation and across all applications. An inconsistency would simply create confusion, not only for users but also for integration. It would make interfaces more complex as application would need to transform the data to its own data structure. Intermediary systems such as API Gateway could used to do transformation; however it would simply move the complexity into such system and with more complex governance as there is a need to track the transformation logic.
</BH>
Two Lessons for DevSecOps from Grounding of 737-MAX
As an IT professional who is working DevSecOps and with strong interest in Aviation industry, I learnt some lessons from the grounding of 737-MAX series.
Automation is Essential but People Need to Know What Automation Does
The crash of ET302 and JT610 might be due to MCAS (Maneuvering Characteristics Augmentation System). The computer reads attitude of the plane and in certain situation it would intervene. It is meant to assist pilots and in ideal situation the pilots would not notice.
In DevSecOps, automation is essential; in fact without automation, it is not possible to achieve DevSecOps. Tools are used to achieve automation.
Use it right and in the hand of good engineers, the tools would do wonder. The DevSecOps would be able to deliver features, fixes, and updates frequently to deliver business values.
US Airway flight US1549 showed how a pilot, Capt. Sully, was able to utilise automation (in the form of auto pilot) to help him to steer the crippled plane before ditching on Hudson River.
In contrast, the computer on Air France flight AF447 provided warning to the pilots that the plane was stalling and approaching terra firma; however the pilots did not respond to the warning and only at last minute it figured out what happened, but it was too late.
In DevSecOps, it is common to mix different tools from different vendors. Each tool has its own strengths and the organisation may have its specific needs and constraints that dictate the tools used.
An engineer who is clue-less on the tools would make DevSecOps fail to deliver its value.
The engineer must be familiar with all of those tools. Using the tools everyday, however, does not make an engineer familiar with the tools; it was simply making the engineer as operator.
The engineer is expected to know how the tools work, how the tools interact to each others, how to exploit each individual tool, how to interpret the errors generated by the tools and how to fix the issues.
Not easy, but at least the engineer could quickly recover the tool-chain when there is/are error[s].
If an engineer is not familiar what each tool in tool-chain does, then he would not know what to do when something unexpected happened. In DevSecOps, it would simply created delays.
Unmanageable Technical Debt will Snowball to Bigger Problem in the Future
The Boeing 737-MAX is the latest variant of the venerable 737 series that started in the 60s. Throughout the years, Boeing kept improving the plane. It accommodate bigger engines, longer airframe (for bigger capacity), etc. It makes the plane still relevant, especially after Airbus rolled out A320s in the 80s.
However, what Boeing has been doing was simply continuously tweaking the plane. As the landing gears are not high, there is a limit on how big the engines 737 could use. Boeing has been tweaking the engine pylons so much that on 737-MAX the pilot needs to be assisted by the MCAS.
The Boeing 737 design has limited the changes that Boeing could do. It has become a technical debt but nothing was done.
Likewise in DevSecOps. While meeting the objective to deliver business values is very important, the technical debt also matters. Delaying addressing the technical debts would simply make the problem bigger and soon or later becomes unmanageable and affecting the business.
It is important for the organisation and DevSecOps team to allocate time and resources to address technical debt. It is either to be done in specific sprints/releases or inserted as part of releases.
IT Strategy
This is my thinking on what I want to do to bring IT Department to provide values to organisation.
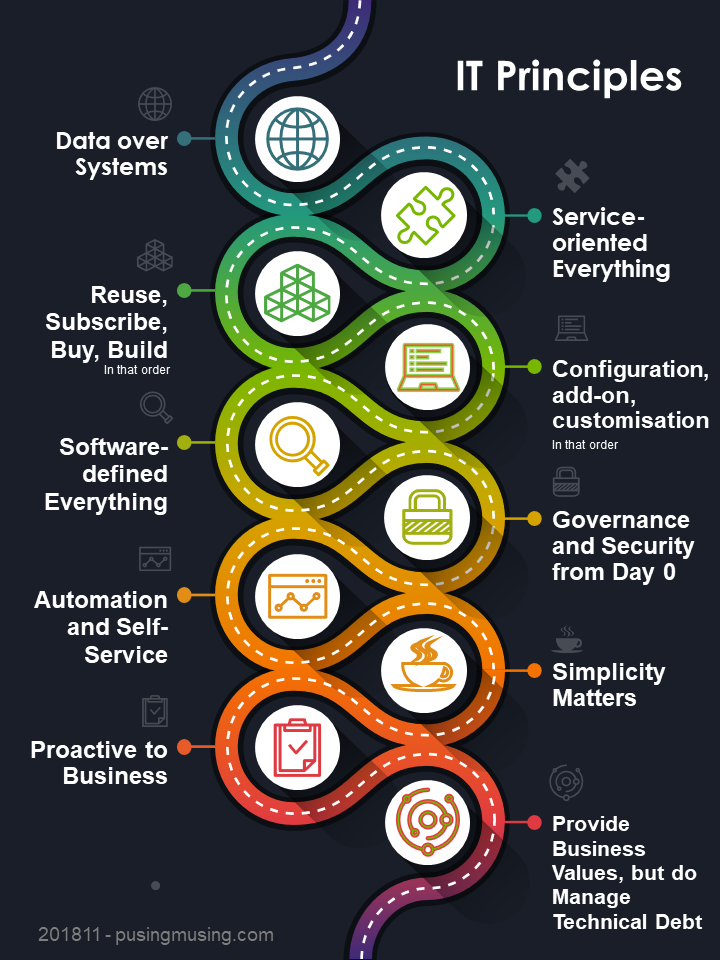
Postscript: changed strategy to principles
Wireless IFE
Recently I flew to Surabaya and took Silk Air (MI) for the return flight. It was a short flight, about 2 hours, and in the evening. I was rather tired, I arrived in Surabaya in the morning (on SQ flight) and spent few hours before flying back. I was looking forward to sleep on the plane.
The last time I took MI was a good 10+ years ago, also for flight to/from Surabaya. So, I did not expect too much from the carrier that some people referred to as “budget airline with SQ fare.”
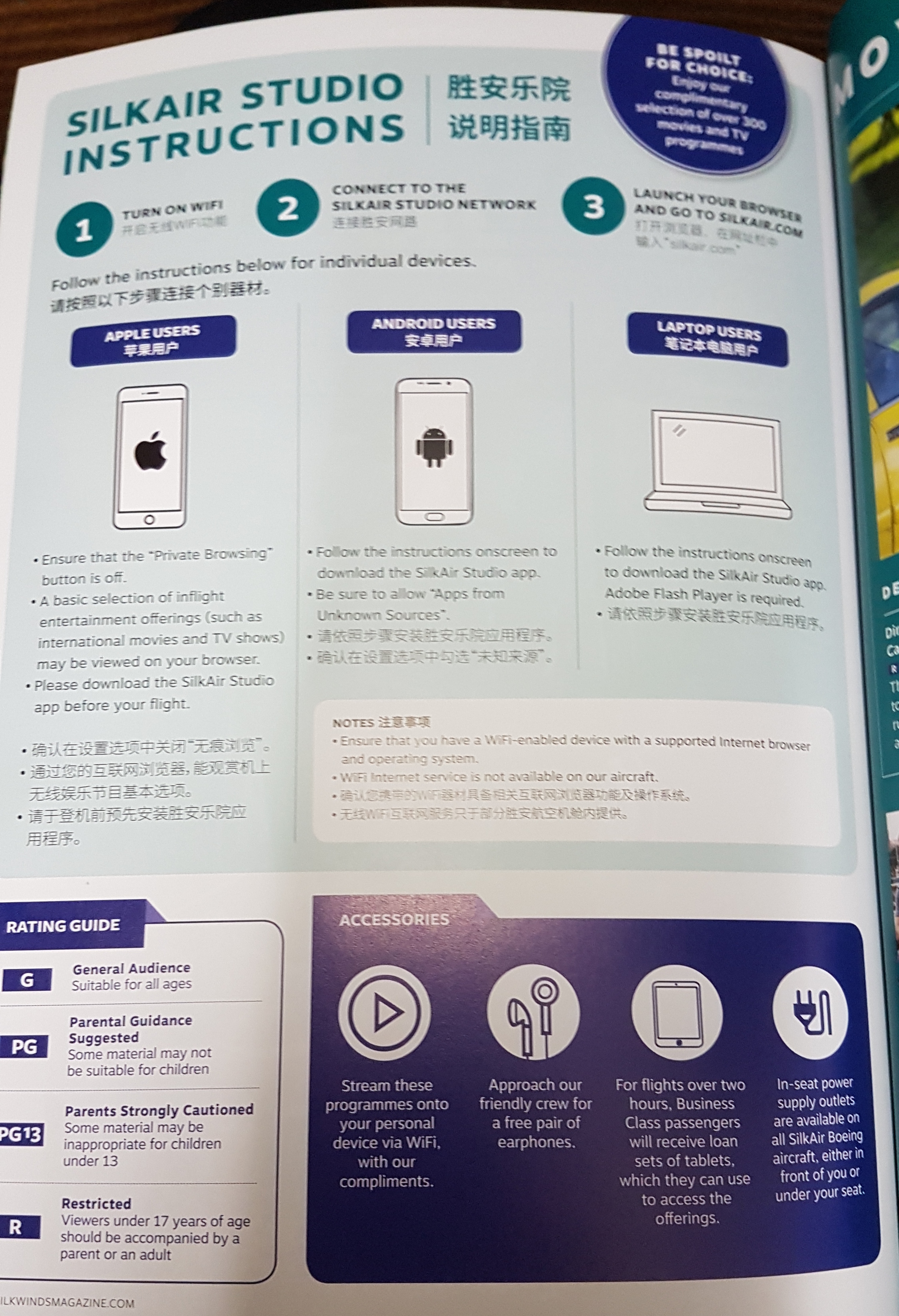
After I boarded the plane, and while waiting for the push back, I browsed the in-flight magazine and noticed now Silk Air provided in-flight entertainment; an improvement. However, the plane had no in-flight entertainment equipment; no LCD screen at the back of the seat. Instead, the movies were streamed to mobile devices through on-board WiFi.
Such setup has becoming very common across many airlines. With everyone has mobile devices and with pervasive access to contents – including movies, many passengers would prefer to watch their own movies on their own devices. For passengers who prefer to watch airline-provided movies, streaming the movies over WiFi saves the airlines lots of money by not having the in-flight entertainment equipment. The absence of such devices also means less weight, less weight means less fuels consumed, which in turn saves the airline more money.
However, I was intrigued by the whole setup on mobile devices in order to access the in-flight entertainment. I took the picture off the page of the in-flight entertainment magazine; and after I touched down in Singapore, I posted the picture on social media, with title ‘SilkAir teaches its passengers how not to do IT security.”
There are two reasons.
For passengers with mobile devices running Android operating system, the magazine instructed the passengers to download the app and then install it directly without going through Google Play Store.
The practice of downloading and installing any applications from any sources other than the official app store is call sideloading; and it is not a recommended practice.
The official Google Play Store, while not perfect, provides some level of protection from malicious app. That may not be the case with an alternative app store or with a website or forum hosting an APK file.
By advising passenger to sideload the application, MI unintentionally is training its passengers to push past all of the warnings that Android displayed.
SilkAir may argue that they could be ‘trusted’. However, such argument simply undermines the education given by IT security professionals: “Do Always download from official stores”.
- The usage of Flash
The magazine also stated that for laptop users, Flash must be enabled in order to enjoy in-flight entertainment.
Good luck for that. Safari, Chrome and Firefox browsers have disabled access to Flash by default. Users must go through myriad setting just to have it enabled, and that only for current session.
Flash was originally a good platform for delivering multimedia content across multiple platforms. The browser plug-in was available on many platform combinations (OS, browsers). Web developer need only to develop the content once, and it was guaranteed to run and work consistently across platforms.
Flash came in the era when browser compatibility was a main issue. Using Flash, web developers could overcome browser compatibility issue with ease.
Now the issue has past with the adoption of HTML5; it could what Flash could natively on the browser, without any plug-ins.
Flash also started to decline after Apple refused to have Flash plug-in on its iOS, and even it went further downhill after strings of vulnerabilities have been discovered on Flash, even up to today. Those issues really pushed browser manufactures to disable Flash [1], [2],[3]; and indeed Adobe itself will terminate Flash support by 2020.
As modern browser has disabled Flash by default, passengers need to tweak the settings in order to enable Flash (and watch the video). It is an inconvenience to passengers; it also showed MI used an old, obsolete, soon-to-be decommissioned platform.
So, what SilkAir can do?
- Silk Air should advise passengers to download the applications ahead, before boarding. Show the instruction on the ticket, or even boarding gate.
When I took Qantas last year to Australia, the website clearly indicates that to enjoy inflight entertaintment in domestic flights, passengers need to install Qantas app.
- Change the technology used to deliver video to HTML5. This will allow any passengers to use their mobile devices, connected to on-board wifi, to access inflight entertainment content with standard browser. It is a much simpler and requires no installation whatsoever.
Post script: after checking many sites, I don’t think Silk Air is unique. KA, TR do provide similar instruction; UA requires Flash plug-in, VA even requiring a more obsolete plug-in: Silverlight. But D8 seems to do it right.
Grain of Rice
I was a bit sceptical upon reading the news on China implanted tiny chip as reported by Bloomberg.
It is rather unbelievable to have such small chip to perform as what claimed. Many chips have many pins, sure whoever needs to implant the chip need to have bigger chip or multiple chips to intercept different signal pins from the motherboard?
Until I came across the article on Light Blue Touchpaper. I learned new concepts such as BMC (Baseboard Management Controller), SPI (Serial-Peripheral Interface) and how the chips are using serial, rather than parallel, signalling; which technically means they need only few wires/pins: data, clock, power and ground. It is also interesting to read that the BMC is an ARM processing running … Linux. We have embedded operating system on a motherboard without even the main OS knows about it.
So, it is technically possible that the tiny chip to modify the signals from BMC. But the question is what’s next. It needs to be able to initiate network call to the Internet and with my limited knowledge this may or may not be possible.
Unless, this chip works ‘together’ with another ‘implant chip’ embedded on the Ethernet port.
To me, the later more makes sense and probably more do-able. Intel had provided the ‘proof’ in 2017, even allowing users to remotely login to the server with embedded KVM software.
With all of these chips, it is possible to have network connection without even the operating system knows about it. People may argue the firewall should block such traffic, there are two main issues with the firewall. With the cloud and hyper-converged solutions, the firewalls are now ‘virtual’. It is a software running on the server itself. Even if there is physical firewall presence, the physical firewall itself may be compromised with implanted chips. Both have the same result: the firewall would not detect and block those extra traffics.
It is a difficult issue to solve. The supply chain is tightly integrated, it is difficult to change the manufacturer. There is no guarantee the US does not do the same. As someone said, it is a matter of choice; which intelligence agency you prefer to have your data: US Intelligence agency or Chinese Intelligence agency 🙂
Cold Call
In my work, it is a ‘routine’ for me to receive cold calls from some companies. The callers either tried to promote their companies or services, did a survey or wanted to send a ‘free’ white paper. Companies could easily find out about my DID number because my number (and so are all my colleagues in the company) is published on the Internet.
Such calls are really annoying. Firstly, unlike junk SMS or junk emails/mails, you cannot simply ignore incoming calls. Even though the calls are from the numbers you don’t know, you don’t know what’s the call about until you pick up the call and listen to what the caller says. It can be disruptive, especially when you are in the middle of work that requires concentration.
I always asked the caller to email me the information and then end the call. I don’t mind to give them my email address, I could simply read those materials anytime or quickly delete them if I don’t find it useful. If I find the materials or services are relevant to me, I would call or email the company for more information.
However, most of callers did not want to stop at email address. They continued asking questions regarding the IT in my company. The main issue with such calls is I have no way to verify the caller. I am acutely aware about social engineering. The caller may be claiming from one company, but what he wanted is to gain insight on my IT infrastructure; such insight may be useful for them to penetrate the IT system.
It does not help that I noticed number of such calls surged after I changed portfolio from Application to Infrastructure. Every day, without fail, I received at least one such cold call.
I prefer to be safe than sorry. I usually asked the caller to drop me email for the questions. If they insisted to continue with questions over the phone, I simply hung up.
But sometimes the callers can be quite daring. One day I received a call claiming that my CIO (Chief Information Officer) had a meeting with his company and my CIO asked him to call me. What puzzled me that the company has been a long vendor with us and my ICO and I just met with their management a week earlier. He asked some questions regarding our infrastructure and he became impatient when I declined to give any information. He even threatened me that he would let my CIO knows that I was not cooperative.
A few minutes later my colleague across the table received the call and from his replies, I could deduce he received similar calls and I quickly gave me the notes that the call should be terminated. Everybody in the division was alerted and true enough almost everyone received such call.
It did not stop there, one month later I received similar call, this time claiming that my Assistant Managing Director (AMD) was the one who asked him to call me. Same pattern, same alert ringing across the division. I joked that at that rate soon the caller would claim that my MD and later chairman asked him to call us. It did not happen, though.